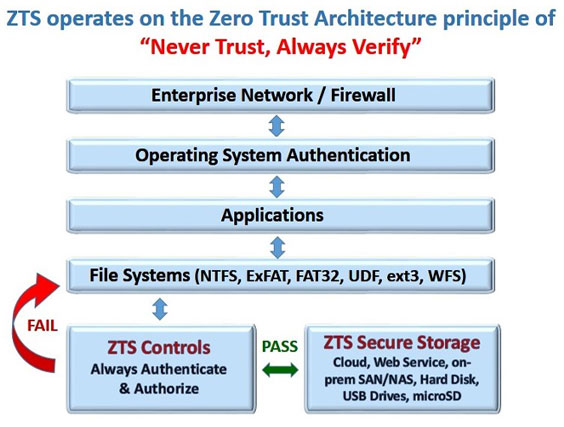
Although the concept of Zero Trust Architecture was introduced several years ago by John Kindervag, VP for Forrester Research, based on the principal of “Never Trust, Always Verify”, it has only recently been gaining popularity in wake of growing cyber-attacks. The National Institute of Standards and Technologies (NIST) defines cyber-security standards, one of which is SP 800-207 “Zero Trust Architecture“.

Used by the NIST National Cybersecurity Center of Excellence (NCCoE) SP 1800-25 and SP 1800-11 for “Data Integrity and Protection from Ransomware and other Destructive Events”. GreenTec is participating in other NIST NCCoE projects including SP 1800-10 for “Protecting Information and System Integrity in Industrial Control System Environments”.
The Zero Trust objective is to put controls in place as close to the Protect Surface as possible, creating a microperimeter to protect it.
Zero Trust Storage™ enforces a microperimiter that automatically defends critical data files and repositories with proven and simple to use defensive controls. Available for the enterprise, in the Cloud, as a private or public Web Service, or provisioned by SAN/NAS on-prem appliances, individual disk devices, USB thumb drives, and microSD devices.
Zero Trust Storage™ simplifies secure remote teleworking for small, medium and large enterprises, maintaining security, trust and confidence in your data with legacy or Cloud apps in AWS, Azure, Google or other service providers with no hidden download fees. A key advantage is that all of the storage devices are customer-owned and controlled with access from any device or app. Remote monitoring and alerting controls and identifies data access, capacity, protection status, retention periods and audit logs.
With conventional storage, encryption only protects from data disclosure. Just because data is encrypted it can still be deleted, re-formatted or re-encrypted by Ransomware causing major data loss.
Whereas, GreenTec’s Zero Trust Storage™ (ZTS) protects from disclosure and also from deletion, modification, or Ransomware with automatic self protecting patented data technologies, and are the secure storage used by the NIST NCCoE for Data Integrity Ransomware Protection.
ForceField Zero Trust Storage Write-Once File System (WFS). Simplified Data Security protects data at the physical block level as it is written in real-time.
Linux Support Zero Trust Storage support for Red Hat Enterprise Linux and Ubuntu have been added. Zero Trust Storage support now includes Windows, RHEL, Ubuntu, CentOS, Debian and others.
XTC-2200 Video Compressor provides significant reduction in wireless bandwidth and storage while maintaining video quality. "Up to 90% reduction with no loss of quality or resolution."
Zero Trust Storage WORMdisks and CYBERdisks Receive Chain Security Analytics Certification "Certified WORMdisks & CYBERdisks strengthen confidence in risk elimination for data and system protection."
DISA Assessment Report GreenTec ZTS WORMdisk and CYBERdisk "The GreenTec WORMdisk product allows for permanent unchangeable storage of data onto a hard disk medium. The CYBERdisk product allows for protection of a boot hard disk where the Master Boot Record (MBR) is unalterable. The two products perform as advertised."
GreenTec-USA Zero Trust Storage WORMdisks key component in NIST Special Publications 1800-11 & 1800-25 Data Integrity Projects for the National Cybersecurity Center Center of Excellence Click here for NIST SP 1800-11 Data Integrity Project Info
GreenTec-USA speaks at AFCEA Cyber Hackathon Protecting data & systems from malicious cyber-security attacks.
GreenTec-USA speaks at Howard University Cyber Hackathon How to make an impact protecting important data from Ransomware and cyber-attacks.
Visit our booth at the DoDIIS Conference on August 1st-3rd in Atlanta, GA Click here for DoDIIS info
Visit us at The National Security Agency (NSA) Towler Road, Fort Meade, MD 20755 At OPS 1 Tech Expo on November 4th, and OPS 2A Tech Expo on November 5th
Visit our booth at the US Cyber Crime Conference on November 14-20th at the Gaylord National Harbor in Maryland just outside Washington, DC.
Feb 19: "High Tech WORMdisk Solution Prevents Equation Cyber Spying Attack and Ransomware" Kaspersky Lab warns of "spying" malware in 30 countries.
Dec 9: ""Virginia Based GreenTec-USA Offers a High Tech Solution That Would Have Prevented Sony Pictures Entertainment's Recent Cyber Attack and Ransomware"
FBI warns of "destructive" malware in wake of Sony attack
Secure Private Customer owned and controlled Zero Trust Storage secures data for on-prem or hosted systems, and in private or hybrid AWS, Azure, Google and other cloud providers. Eliminates expensive data download costs. Implements simple browser-based web access with encryption/decryption protection from any device anywhere for financial transactions, video, digital evidence, permanent records, industrial control systems, voting machines and other secure data. Solves chain-of-custody issues. Provides the ability to deliver ORIGINAL DIGITAL DATA when needed for records retention or digital evidence in court.